Endpoint Security in an AI World: Protecting Devices Against Smarter Attacks
DR
Your Devices Are Now on the Front Line
If your business handles sensitive customer, client, or patient data, your laptops and phones are now as critical as your front door locks. Every email, app, and remote login is a possible entry point for an attacker using artificial intelligence to move faster than your IT policies. AI has supercharged both sides of cybersecurity—defenders and attackers—but attackers only have to be right once.
Recent reports estimate that AI‑enabled cyberattacks have surged more than 70% year over year, with AI‑generated phishing lures driving unprecedented click‑through rates and breach costs climbing into the millions per incident. For a bank, law firm, medical practice, or sports organization, that’s not an abstract risk—it’s a business continuity issue. In this post, you’ll see how endpoint security in an AI world really works, why “old-school” protection isn’t enough, and what practical steps you can take to feel confident your data is truly protected.
The New Reality: AI Has Changed the Rules of Cyber Risk
AI hasn’t just made attacks more common; it has made them more convincing, more automated, and much harder for humans to spot in time.
Security researchers estimate that global AI‑driven cyberattacks are projected to surpass 28 million incidents in 2025, a 72% year‑over‑year increase. One analysis found phishing campaigns surged over 1,200% due to generative AI, and AI‑assisted attacks are responsible for a growing share of breaches worldwide. Another 2025 report suggests that more than 80% of phishing emails are now created with AI, dramatically increasing the odds that a busy professional will accidentally click.
For privacy‑regulated sectors such as healthcare, finance, and insurance, the impact is already visible. In 2025, healthcare alone saw multiple breaches involving hundreds of thousands to tens of millions of individuals, with data such as medical details, Social Security numbers, and financial information exposed. The Change Healthcare ransomware incident disrupted claims processing across the United States and led to a multimillion‑dollar ransom payment after sensitive health and financial data was exfiltrated. These are not just IT problems; they trigger regulatory scrutiny, reputational damage, and operational chaos.
Thing to remember: Cybersecurity that doesn’t account for AI is like driving with last year’s map—the roads have changed, and the shortcuts belong to the attackers now.
Why Endpoint Security Is the New “Business Insurance”
When people think “cybersecurity,” they often picture a big firewall in a data center. But in 2026, the real battles are happening on endpoints—laptops, tablets, phones, and cloud‑connected devices that employees use every day.
AI‑enabled attackers love endpoints because that’s where humans interact with systems. AI makes it cheaper and faster to create tailored phishing emails, realistic deepfake voice calls, and malicious attachments that adapt to the victim’s defenses. Industry reports show that phishing remains one of the top attack methods in cloud environments, and AI has only boosted its effectiveness. That means one distracted click on a work laptop can expose an entire practice or firm.
Here’s the important mindset shift: endpoint security is not an IT upgrade—it’s a basic business safeguard, like insurance or payroll tax compliance. You wouldn’t operate a medical practice without malpractice insurance, or a law firm without professional liability coverage. In the same way, you cannot responsibly run a privacy‑bound organization without robust, AI‑aware endpoint protection and vulnerability management.
Think of endpoint security and vulnerability management as:
- A “check engine light” for your devices, constantly scanning for weaknesses before attackers find them.
- An automated triage nurse, prioritizing which issues matter most so your team isn’t overwhelmed.
- A quiet, always‑on alarm system that notices when behavior on a device suddenly looks “off” and reacts in seconds, not days.
Key insight: Cyber attacks are now far more sophisticated, so your protection has to be at least as smart—and preferably smarter.
How AI Is Attacking Your Endpoints (In Plain English)
You don’t need to be technical to understand how AI is being used against your organization. You just need to recognize the patterns.
Common AI‑powered techniques now hitting endpoints include:
- Hyper‑realistic phishing emails
AI tools generate emails that match your clients’ tone, reference real projects, and even imitate internal writing styles to trick employees into clicking malicious links. - Deepfake voice and video “urgent” requests
Attackers can synthesize an executive’s or doctor’s voice to call someone in finance and request a wire transfer or data export—“right now, no time for questions.” - Smart malware that learns as it goes
Some botnets and malware families now incorporate machine learning to change behavior on the fly and evade traditional antivirus tools. - Automated reconnaissance on your devices
AI can rapidly scan a device or cloud workspace for misconfigurations, weak passwords, unpatched software, and exposed credentials, turning minor gaps into major footholds.
Regulators and standards bodies are taking this seriously. The U.S. National Institute of Standards and Technology (NIST) has released a draft Cybersecurity Framework Profile for Artificial Intelligence that helps organizations secure AI systems, use AI for defense, and thwart AI‑enabled attacks. NIST notes that its AI profile is intended to help organizations “understand, examine and address the cybersecurity concerns related to AI and thoughtfully integrate AI into their cybersecurity strategies.”
Bottom line: If the attacks are using AI and your defenses are not, the playing field is tilted—and not in your favor.
Smart Protection: What Modern Endpoint Security Looks Like
Let’s translate the jargon into what actually matters for a bank, law firm, clinic, or sports organization that handles sensitive personal data. Modern endpoint security in an AI world has three big pillars: visibility, intelligence, and response.
1. Visibility: Know what you have and where it’s vulnerable
You cannot protect what you cannot see.
- Maintain a live inventory of all devices that access client or patient data (including personal laptops used for remote work).
- Continuously scan these endpoints for missing patches, risky software, and misconfigurations—especially those connected to cloud services and AI tools.
- Map vulnerabilities to business impact: a receptionist’s kiosk and a billing laptop do not carry the same risk.
AI‑aware vulnerability management platforms now help organizations prioritize which issues to fix first, instead of producing overwhelming lists of technical problems. This matters for smaller teams who do not have a full‑time security staff but still face enterprise‑level threats.
2. Intelligence: Use AI on your side
The good news is that AI is also powering better defenses.
NIST’s new AI‑focused guidance highlights “conducting AI‑enabled cyber defense” as a key focus area, encouraging organizations to use AI to enhance threat detection, automated response, and risk management. For endpoints, that looks like:
- Behavioral monitoring that spots unusual login patterns, file access, or app behavior.
- AI‑driven detection that can recognize phishing attempts and malicious attachments in real time.
- Automated correlation across many devices to see an attack unfolding, rather than treating each alert as isolated.
In other words, your security tools should be just as curious and relentless as the attackers’ AI agents.
3. Response: Contain issues before they become incidents
Speed is everything once a device is compromised.
Recent high‑profile breaches show that days‑long detection delays can massively amplify the damage and cost of an incident. Modern endpoint protection should allow you to:
- Isolate a suspicious device from the network in clicks, not hours.
- Roll back malicious changes on endpoints where possible.
- Generate clear, non‑technical incident summaries your leadership and regulators can understand.
Key insight: The goal isn’t “perfect security”—it’s fast, intelligent containment that turns potential disasters into minor, recoverable events.
A Relatable Scenario: When AI Meets a Busy Workday
Imagine this scenario.
You run a mid‑sized specialty medical practice or regional law firm. Mornings are chaos. Email, patient portals or client portals, billing systems, and cloud tools all demand attention at once. A senior partner or physician is double‑booked. Someone in billing is working from a personal laptop “just for today.”
Into that environment lands:
- A perfectly written email that looks like it’s from your major insurer or banking partner, asking you to “urgently verify claim data” with a link.
- A PDF attachment that appears to be an updated contract from a known client.
- A voicemail that uses a synthetic version of a doctor’s or partner’s voice asking a staff member to “send over the latest reconciliation file” to a new email address “because IT is working on the main account.”
Every one of these is trivial to generate with today’s AI tools. And if one employee clicks while using a device that’s missing security patches or running outdated antivirus, that single moment can become a reportable breach affecting tens of thousands of records. In recent healthcare and insurance incidents, attackers accessed data over multiple days before detection, exposing a mix of medical, financial, and identity information.
Now contrast that with a practice or firm that has modern, AI‑aware endpoint protection and vulnerability management in place—supported by a partner like CyberSecurity1st.
- Endpoints are continuously assessed for vulnerabilities tied to the real risk of data exposure.
- AI‑driven monitoring flags the suspicious email and blocks the malicious PDF before it ever opens.
- Anomalous activity on a billing laptop triggers automatic containment and an alert that’s actually readable, not a 50‑page log dump.
Your team goes back to work, maybe mildly annoyed at the blocked file—but your data is intact, your regulators are unalarmed, and your clients or patients never even hear about the near‑miss.
Thing to remember: In an AI‑driven threat landscape, peace of mind doesn’t come from hoping people never make mistakes; it comes from designing your endpoint security so that ordinary mistakes don’t become headlines.
Taking the Next Step: From Concern to Confidence
You don’t need to turn your business into a security company. You just need to treat cybersecurity—especially at the endpoint level—the same way you treat other critical safeguards: with a budget, a plan, and expert help.
Leading guidance from organizations like NIST shows a clear path: understand how AI is changing the threat landscape, use AI to strengthen your defenses, and continually manage vulnerabilities across your systems. For privacy‑bound organizations, partnering with specialists who live and breathe this world turns a vague fear of “hackers and AI” into a concrete, managed risk. That translates into something you can actually feel: confidence in the safety of your data.
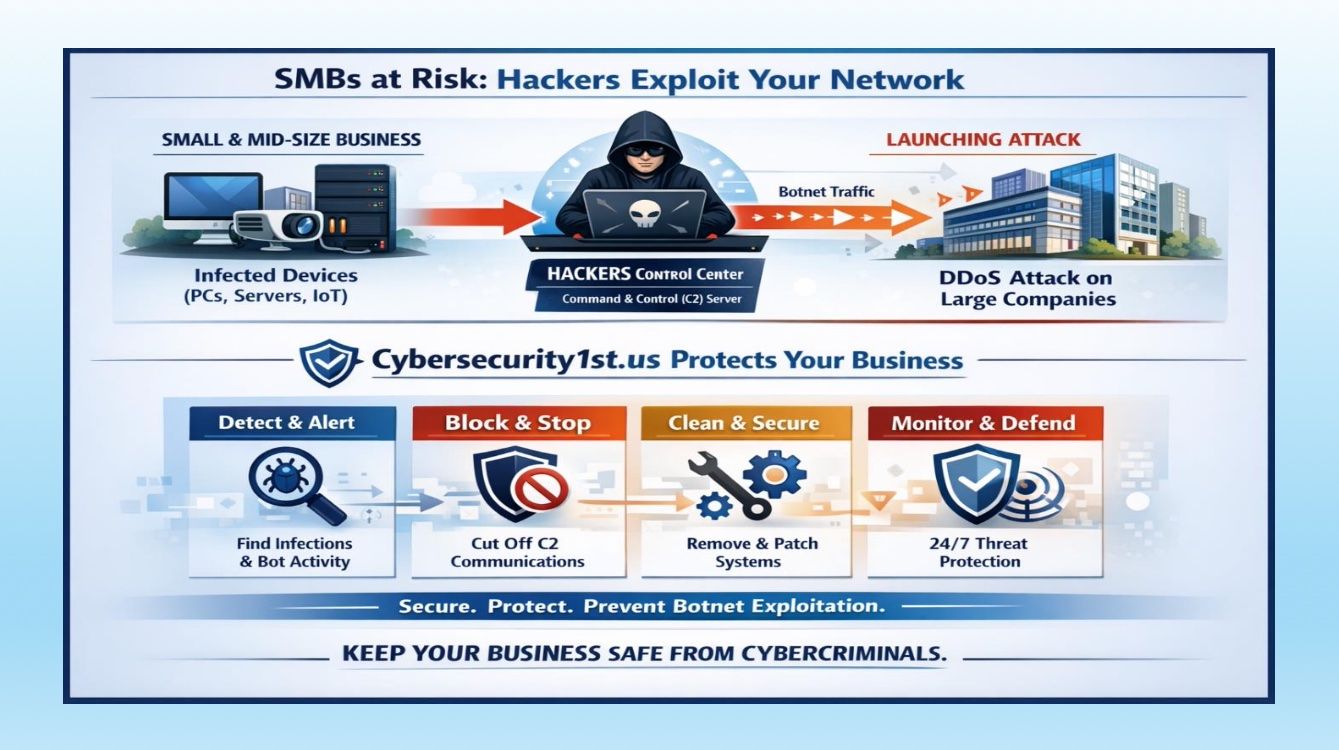
CyberSecurity1st focuses specifically on helping small and medium‑sized organizations—like banks, law firms, medical practices, and sports organizations—get practical, AI‑aware vulnerability management and endpoint protection in place without needing a giant internal security team. The goal isn’t to flood you with buzzwords. It’s to quietly make sure your devices, data, and workflows stay out of the breach news cycle so your team can focus on serving clients and patients.
If this sparked some curiosity—or a healthy sense that your current protections might be stuck in a pre‑AI era—take 60 seconds before you move on:
- Jot down one endpoint risk you’re now aware of (like personal laptops, or unmanaged tablets).
- Share this post with one colleague who “owns” technology or compliance.
- When you’re ready, schedule a short consultation with CyberSecurity1st to see what AI‑aware vulnerability management would look like in your environment.
Your future self—the one who never has to send a “we regret to inform you about a data breach” email—will be grateful.

#CyberSecurity1st #CyberSecurity #infosec #databreach #cloudsecurity #datasecurity #endpointsecurity #AIsecurity #healthcareIT #finservsecurity
References:
- TotalAssure – “AI Cybersecurity Statistics in 2025: Comprehensive Data” (2026).
- The Network Installers – “AI Cyber Threat Statistics: The 2025 Landscape of AI‑…” (2025).
- DeepStrike – “AI Cyber Attack Statistics 2025, Trends, Costs, Defense.”
- Programs.com – “New Report: Over 80% of Cyberattacks Now Use AI” (2025).
- Fortinet – “Cybersecurity Statistics 2025: Rising Threats and Industry …”
- HIPAA Journal – “Largest Healthcare Data Breaches of 2025” (2026).
- Security Magazine – “Top 20 Healthcare Data Breaches of 2025” (2026).
- Nixon Peabody – “The Change Healthcare cybersecurity breach: Impact on healthcare providers” (2025).
- NIST / NISTIR 8596 – “Cybersecurity Framework Profile for Artificial Intelligence (Draft)” and related guidance (2025).
- CyberDefenseMagazine & related AI‑attack trend reporting (2025).
